
Safeguarding Against Outsourcing Security Risks: Strategies for Mitigation
In different articles, we have explored why Outsourcing has become a prevalent practice for many businesses looking to streamline operations, reduce costs, and access specialized skills and recently provided a “Guide to select the Outsourcing method”. However, along with its benefits, outsourcing also brings security risks that must be carefully managed. This article explores the outsourcing security risks associated with outsourcing and provides strategies for mitigating these risks.
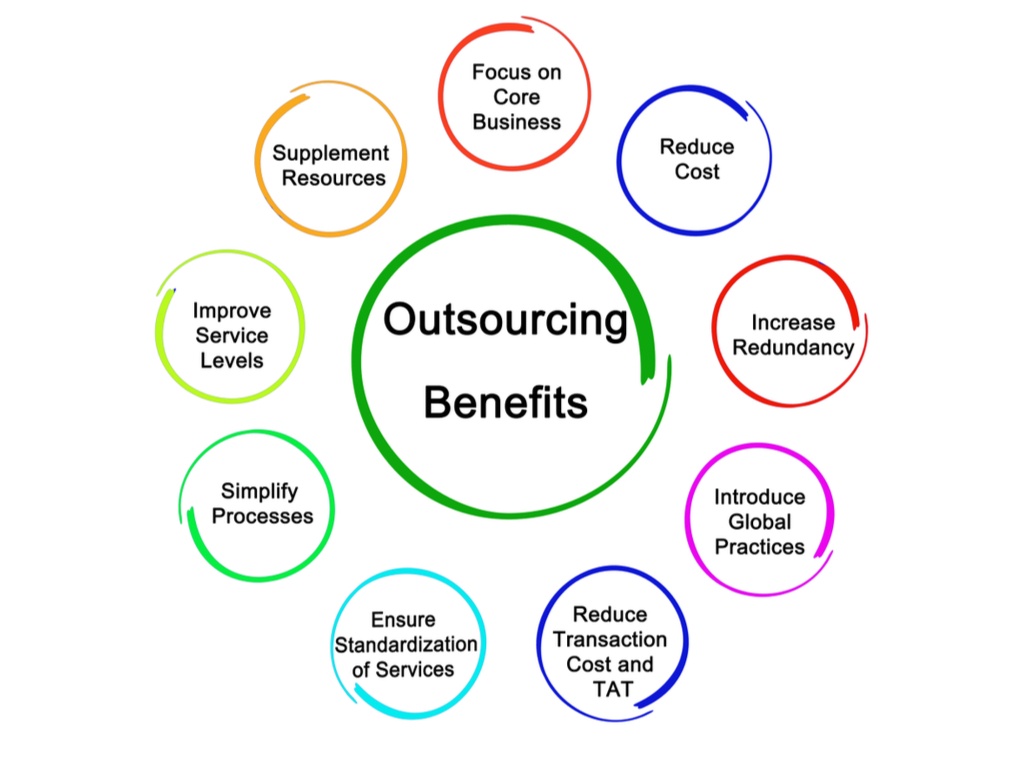
Benefits of outsourcing software developments
The image below summarizes the benefits of outsourcing which is the reason why this practice is growing year after year.
Outsourcing Security Risks
There are five main outsourcing security challenges that the company using outsourcing the service must be aware of:
Data Breaches: When sensitive data is shared with third-party vendors, there is a risk of data breaches. This situation can occur due to inadequate security measures on the part of the vendor or malicious actions by insiders.
Loss of Intellectual Property: Outsourcing may involve sharing proprietary information with third parties, increasing the risk of intellectual property theft.
Compliance and Regulatory Risks: Outsourcing may lead to compliance and regulatory risks if the vendor fails to adhere to relevant laws and regulations, potentially resulting in legal penalties.
Dependency Risks: Over-reliance on a single vendor for critical functions can create dependency risks, making the business vulnerable to disruptions if the vendor fails to deliver.
Reputation Risks: Security breaches or other incidents involving outsourced functions can damage a business’s reputation, leading to loss of customer trust and business opportunities.
7 Strategies for Mitigating Outsourcing Security Risks
In our experience, seven strategies prevent damages stemming from security breaches in the outsourcing company.
Conduct Due Diligence: Before engaging a vendor, conduct thorough due diligence to assess their security practices, compliance with regulations, and track record in handling sensitive information.
Establish Clear Contracts: The outsourcing contract should clearly define security requirements, including data protection measures. It should also include clauses for periodic security audits and compliance checks.
Implement Strong Access Controls: Limit access to sensitive data and systems to authorized personnel only. Use multi-factor authentication and regular access reviews to prevent unauthorized access.
Encrypt Sensitive Data: Encrypt data both in transit and at rest to protect it from unauthorized access. Ensure security management of encryption keys.
Monitor Vendor Performance: Continuously monitor the vendor’s performance to ensure that they meet security requirements. Implement mechanisms for reporting and addressing security incidents promptly.
Create a Contingency Plan: Develop a contingency plan to mitigate the impact of a security breach or vendor failure. This plan should include procedures for quickly switching to alternate vendors if needed.
Employee Training: Regularly train employees on best security practices and the importance of data protection when working with outsourced vendors.
Conclusion
Outsourcing can offer numerous benefits to businesses but also has inherent security risks. By implementing the strategies outlined above, Deproinf can effectively mitigate these risks and ensure the security of the customer’s sensitive information outsourced.
I hope this article about Outsourcing Security risks has been helpful to you. If you liked it or want to learn more about Deproinf, please subscribe to stay updated.
If you have specific needs please GIVE US YOUR INFORMATION and we will contact you as soon as possible.

